The surprising number of static data masking use cases requires bullets to present them. These first three use cases begin with “masking sensitive data”:
- Prior to third-party data sharing
- In databases shared with development, QA, research or analytics
- Prior to adding a data set to a data lake or big data environment
And here are more:
- Preparing a database for tokenization or encryption deployment
- Rekeying data in a database following a new key version or key rotation
- Data protection step in Extract, Transform and Load (ETL) operations
These are just a few. You will find many uses for static data masking.
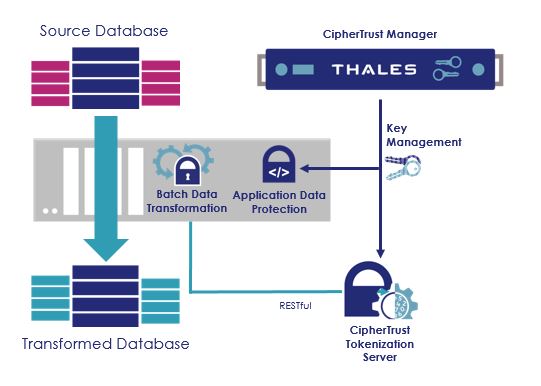
Batch Data Transformation is a powerful tool that gives you high-performance static data masking as part of the CipherTrust Data Security Platform. It leverages the power of CipherTrust Application Data Protection and CipherTrust Tokenization to protect vast quantities of data quickly.
Secure, cost-effective static data masking
Not every static data masking solution is secure. With Batch Data Transformation, you can depend on the security of centralized key management provided by CipherTrust Manager, which can provide up to FIPS 140-2 Level 3 key security. Meanwhile, every investment in the Data Security Platform makes it more valuable to you.
Accelerate Transformation of Existing Sensitive Data
Following deployment and execution of CipherTrust Data Discovery and Classification you can rapidly protect discovered sensitive information in database columns quickly and efficiently using either encryption or tokenization with minimal disruption, effort and cost.
Enable database sharing with reduced risk
Static data masking enables you to remove the sensitive information before sharing with internal or third-party developers and big data environments while simultaneously maintaining your data integrity and supporting mission-critical testing and analytical activities.
Static Data Masking where you need it
Batch Data Transformation and its data protection tools are all software and completely cloud friendly. You can mask data on premises and use it in the cloud, mask data in the cloud and use it there, or secure data in one cloud and use it in another. The CipherTrust Data Security Platform provides a wide range of data protection capabilities from on-premises to cloud, enabling secure digital transformations.
Efficient Encryption
Large volumes of data are encrypted quickly with Batch Data Transformation in conjunction with CipherTrust Application Data Protection. Policy files define encryption options including standard AES encryption or format preserving encryption, while identifying the database columns to be protected and the number of records in each batch.
Flexible Tokenization
An alternative to encryption for static data masking is tokenization. Batch Data Transformation can utilize the CipherTrust Tokenization Server to tokenize select database columns. Detokenization is supported so that applications can access the clear data again when required, or, irreversible tokenization can ensure that third parties never gain access to original sensitive data.
Flexible Conversion Between Data Stores
CipherTrust Batch Data Transformation can protect data while it is moving, for example, from a database to various flat file formats or in reverse.
Data Transformation Options
- Cipher Block Chaining using the AES-CBC-PAD encryption mode
- Format Preserving Encryption (FPE) with ASCII and Unicode character set options
- Format preserving alpha/numeric
- Tokenization, reversible or irreversible
Source and Destination Transformation Options
- Database to database
- Flat file (CSV) to database
- Database to flat file
- Flat file to flat file
Hardware and Operating System Requirements
- Processor with 4 cores, 16GB RAM (minimum)
- Java Runtime Environment (JRE)
- Windows
- Linux – RedHat, CentOS, Ubuntu and SUSE
