 Detailed, Actionable Data Security Intelligence
Detailed, Actionable Data Security Intelligence
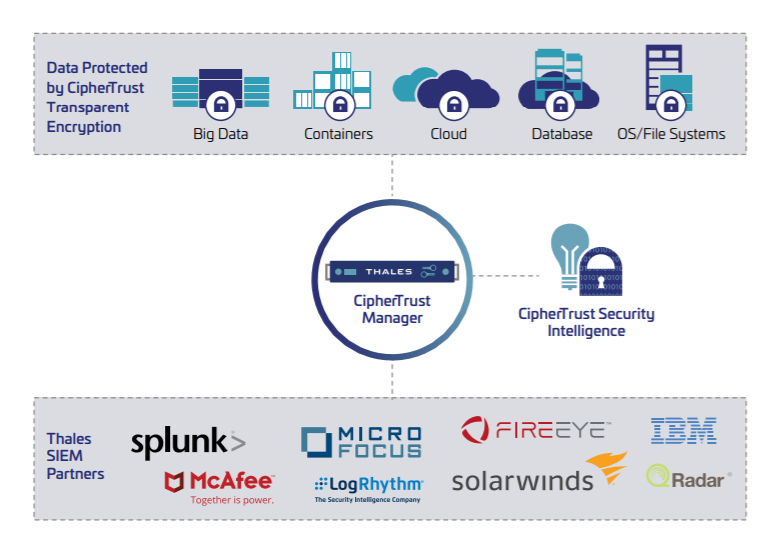
CipherTrust Transparent Encryption delivers detailed data access audit logs, which are useful for compliance, identifying unauthorized access attempts, and building baselines of authorized user access patterns. CipherTrust Security Intelligence logs and reports streamline compliance reporting and speedup threat detection using leading Security Information and Event Management (SIEM) systems. The solution allows immediate automated escalation and response to unauthorized access attempts and provides all the data needed to build behavioral patterns required to identify suspicious usage by authorized users.