| Image | Title | Categories | Link | hf:doc_categories |
|---|---|---|---|---|
| 2023 Thales Cloud Security Study | ||||
| Achieving Security and Compliance for SAP HANA with CipherTrust Transparent Encryption | CipherTrust, CipherTrust Integrations | ciphertrust ciphertrust-integrations integrations | ||
| Advanced data protection for AWS S3 with CipherTrust Transparent Encryption Solution Brief | CipherTrust Integrations, Cloud Security, Integrations | ciphertrust-integrations cloud-security integrations | ||
| AppViewX and Thales Trusted Cyber Technologies Luna Network HSM Solution Brief | ||||
| Avoiding Amazon S3 Data Leaks with Scalable Encryption and Access Controls Solution Brief | CipherTrust Integrations, Cloud Security, Integrations | ciphertrust-integrations cloud-security integrations | ||
| Cipher Summit Resource Hub | Cipher Summit | cipher-summit | ||
| CipherTrust Cloud Key Management Solutions for Amazon Web Services Solution Brief | CipherTrust, CipherTrust Integrations, Cloud Security | ciphertrust ciphertrust-integrations cloud-security integrations | ||
| CipherTrust Cloud Key Manager for SAP Applications | CipherTrust, CipherTrust Integrations | ciphertrust ciphertrust-integrations integrations | ||
| CipherTrust Cloud Key Manager Product Brief | CipherTrust, Cloud Security | ciphertrust cloud-security | ||
| CipherTrust Data Discovery and Classification Walkthrough | Video | video | ||
| CipherTrust Data Protection Gateway Product Brief | CipherTrust | ciphertrust | ||
| CipherTrust Data Security Platform Data Sheet | CipherTrust | ciphertrust | ||
| CipherTrust Data Security Platform Product Brief | CipherTrust | ciphertrust | ||
| CipherTrust Data Security Platform Self Guided Tour | CipherTrust, Video | ciphertrust video | ||
| CipherTrust Encryption key management solutions for Microsoft® SQL Server® and Oracle® Database Solution Brief | CipherTrust | ciphertrust | ||
| CipherTrust Live Data Transformation Product Brief | CipherTrust | ciphertrust | ||
| CipherTrust Manager k160 Product Brief | CipherTrust | ciphertrust | ||
| CipherTrust Manager k570 Product Brief | CipherTrust | ciphertrust | ||
| CipherTrust Manager Product Brief | CipherTrust | ciphertrust | ||
| CipherTrust Platform Community Edition | CipherTrust | ciphertrust | ||
| CipherTrust Security Intelligence Product Brief | CipherTrust | ciphertrust | ||
| CipherTrust Teradata Protection Solution Brief | CipherTrust, CipherTrust Integrations | ciphertrust ciphertrust-integrations integrations | ||
| CipherTrust Tokenization for SAP ERP Solutions | CipherTrust, CipherTrust Integrations | ciphertrust ciphertrust-integrations integrations | ||
| CipherTrust Transparent Encryption for Kubernetes Product Brief | CipherTrust | ciphertrust | ||
| CipherTrust Transparent Encryption for Teradata Vantage Solution Brief | CipherTrust Integrations, Integrations | ciphertrust-integrations integrations | ||
| CipherTrust Transparent Encryption Product Brief | CipherTrust | ciphertrust | ||
| CipherTrust Transparent Encryption Ransomware Protection | CipherTrust | ciphertrust | ||
| CM7 Network Manager Product Brief | Network Encryption | network-encryption | ||
| CN4010 Product Brief | Network Encryption | network-encryption | ||
| CN4020 Product Brief | Network Encryption | network-encryption | ||
| CN6010 Product Brief | Network Encryption | network-encryption | ||
| CN6100 Product Brief | Network Encryption | network-encryption | ||
| CN6140 Product Brief | Network Encryption | network-encryption | ||
| CN9120 Product Brief | Network Encryption | network-encryption | ||
| Cohesity | ||||
| CTERA Enterprise File Services Platform and Thales TCT CipherTrust Manager Solution Brief | CipherTrust Integrations, Integrations | ciphertrust-integrations integrations | ||
| CTO Sessions Webcast On Demand: Zero Trust – Beyond the Buzzword | Webcast, Zero Trust | webcast zero-trust | ||
| CTO Sessions On Demand Webcast: Everything You Need to Know About Phishing-Resistant MFA | Identity & Access Management, Webcast | identity-access-management webcast | ||
| CTO Sessions On Demand: Are You Quantum Ready? | Quantum, Webcast | quantum webcast | ||
| CTO Sessions On Demand: Best Practices for Data in Transit Encryption | Network Encryption, Webcast | network-encryption webcast | ||
| CTO Sessions On Demand: Data Protection at the Edge | Edge Solutions, Webcast | edge-solutions webcast | ||
| CTO Sessions On Demand: Preventing Ransomware in Microsoft 365 Environments | Votiro, Webcast | votiro webcast | ||
| CTO Sessions On Demand: Protecting Your Data in Their Cloud | CipherTrust, Cloud Security, Webcast | ciphertrust cloud-security webcast | ||
| CTO Sessions On Demand: Securing the Convergence of HPC and AI in the Enterprise | CipherTrust, CipherTrust Integrations, Webcast | ciphertrust ciphertrust-integrations webcast integrations | ||
| CTO Sessions Webcast On Demand: AI & Cybersecurity | Votiro, Webcast | votiro webcast | ||
| CTO Sessions Webcast On Demand: Building a Root of Trust in How to Secure the Most Sensitive Data | HSM, Webcast | hsm webcast | ||
| CTO Sessions Webcast On Demand: Deliver Secure Hyper-Converged Infrastructure Solutions | CipherTrust, Webcast | ciphertrust webcast | ||
| CTO Sessions Webcast On Demand: HSM Boot Camp – A Guide to HSM Deployments from the Core to the Cloud to the Edge | HSM, Webcast | hsm webcast | ||
| CTO Sessions Webcast On Demand: Network Encryption Boot Camp – A Guide to Network Encryption from the Core to the Cloud to the Edge | Network Encryption, Webcast | network-encryption webcast | ||
| CTO Sessions Webcast On Demand: Taking Control of 2023’s Top Tech Trends | Cloud Security, Edge Solutions, Network Encryption, Quantum, Webcast, Zero Trust | cloud-security edge-solutions network-encryption quantum webcast zero-trust | ||
| CTO Sessions Webcast On Demand: Top 10 Reasons to Protect Your Agency with CipherTrust Data Security Platform | CipherTrust, Webcast | ciphertrust webcast | ||
| CTO Sessions Webcast: A Guide to BYOK and HYOK for AWS, Azure, Google, Oracle and More | Cloud Security, Webcast | cloud-security webcast | ||
| CTO Sessions Webcast: Word on the Street – 2024’s Top Tech Trends | Webcast | webcast | ||
| CTO Sessions: Quantum Resistant Security | Webcast | webcast | ||
| CV1000 Product Brief | Network Encryption | network-encryption | ||
| Cyber EO Compliance Video Series – Part 2 – Multi-Factor Authentication | Compliance, Video | compliance video | ||
| Cyber EO Compliance Video Series – Part 3 – Data at Rest Encryption | Compliance, Webcast | compliance webcast | ||
| Cyber EO Compliance Video Series – Part 4 – Data in Transit Encryption | Compliance, Video | compliance video | ||
| Cyber EO Compliance Video Series – Part 5 – Securing Cloud Deployments | Compliance, Video | compliance video | ||
| Cyber EO Compliance Video Series – Part 6 – Implementing a Zero Trust Architecture | Compliance, Video | compliance video | ||
| Data Discovery & Classification Product Brief | CipherTrust | ciphertrust | ||
| Data Discovery & Classification Solution Brief | CipherTrust | ciphertrust | ||
| Data Protection Solutions for the Edge Solution Brief | Edge Solutions | edge-solutions | ||
| Dell PowerProtect Cyber Recovery and Thales CipherTrust Manager | CipherTrust, CipherTrust Integrations | ciphertrust ciphertrust-integrations integrations | ||
| DoD STIG Compliance Virtualization-Based Security – External Key Management Solution Brief | CipherTrust, Compliance | ciphertrust compliance | ||
| eBook: Encrypt Everything | White Paper | white-paper | ||
| eBook: High Speed Ethernet WAN | Network Encryption, White Paper | network-encryption white-paper | ||
| eBook: Ryuk: Everything You Need to Know About the Ransomware Targeting U.S. Governments & Government Agencies | Votiro | votiro | ||
| eBook: The Comprehensive Guide on Phishing-Resistant MFA, Passkeys and FIDO security keys. | Identity & Access Management | identity-access-management | ||
| Enterprise Key Management for NetApp Solution Brief | CipherTrust, CipherTrust Integrations, Integrations | ciphertrust ciphertrust-integrations integrations | ||
| Enterprise Key Management Solutions for KMIP Clients, TDE and LUKS Solution Brief | CipherTrust | ciphertrust | ||
| Entrust and Thales TCT HSMs Solution Brief | ||||
| FCW/NetGov’s Zero Trust Workshop Replay: Zero Trust: Buzzword to Brass Tacks | Video, Zero Trust | video zero-trust | ||
| HID ActiveID and Thales TCT Luna Network HSM Solution Brief | HSM Integrations, Integrations | hsm-integrations integrations | ||
| How Ransomware attacks leverage unprotected RDPs Solution Brief | Identity & Access Management | identity-access-management | ||
| How to Integrate UiPath with Thales TCT’s Luna Credential System | LCS Integrations, Luna Credential System, Video | lcs-integrations luna-credential-system video integrations | ||
| HPE 3PAR StoreServ and Thales CipherTrust Manager | CipherTrust, CipherTrust Integrations, Integrations | ciphertrust ciphertrust-integrations integrations | ||
| HPE GreenLake and Thales TCT CipherTrust Data Security Platform | CipherTrust, CipherTrust Integrations, Integrations | ciphertrust ciphertrust-integrations integrations | ||
| HPE servers and storage with Thales CipherTrust Data Security Platform Solution Brief | CipherTrust, CipherTrust Integrations, Integrations | ciphertrust ciphertrust-integrations integrations | ||
| Industry Insight: Supply Chain Risk Management | White Paper | white-paper | ||
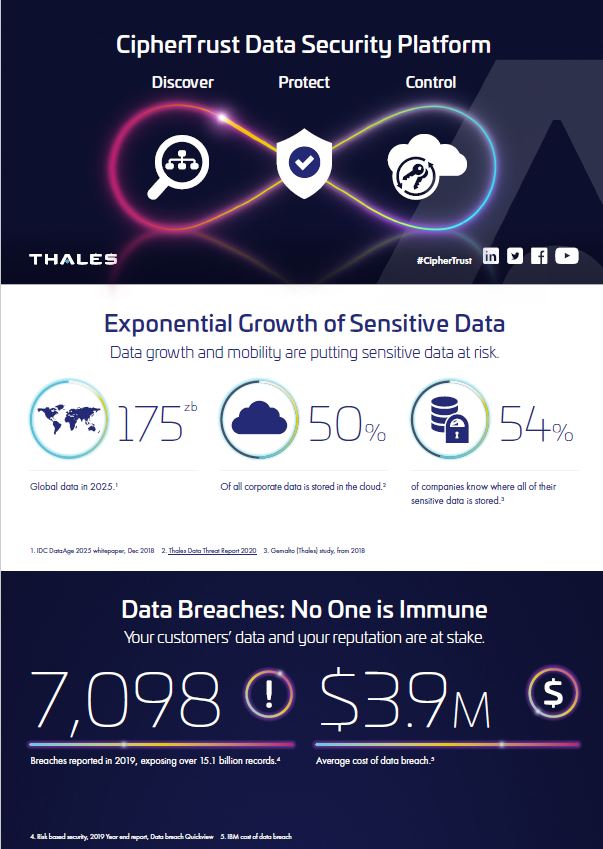
| Infographic: CipherTrust Data Security Platform Infographic | CipherTrust | ciphertrust | ||
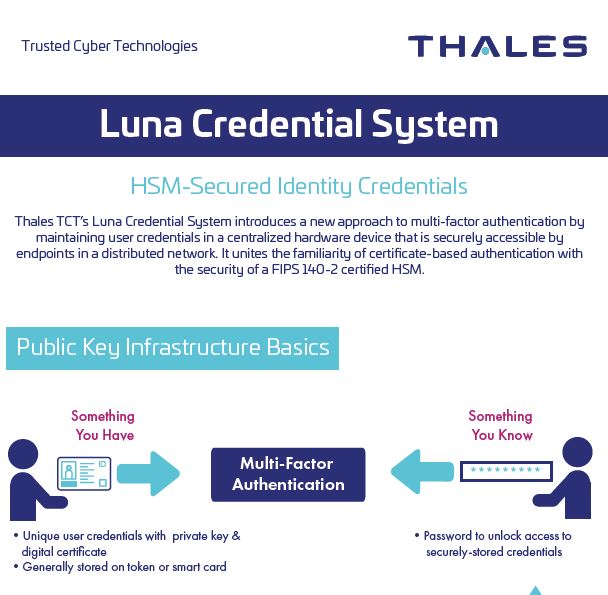
| Infographic: Luna Credential System | Luna Credential System | luna-credential-system | ||
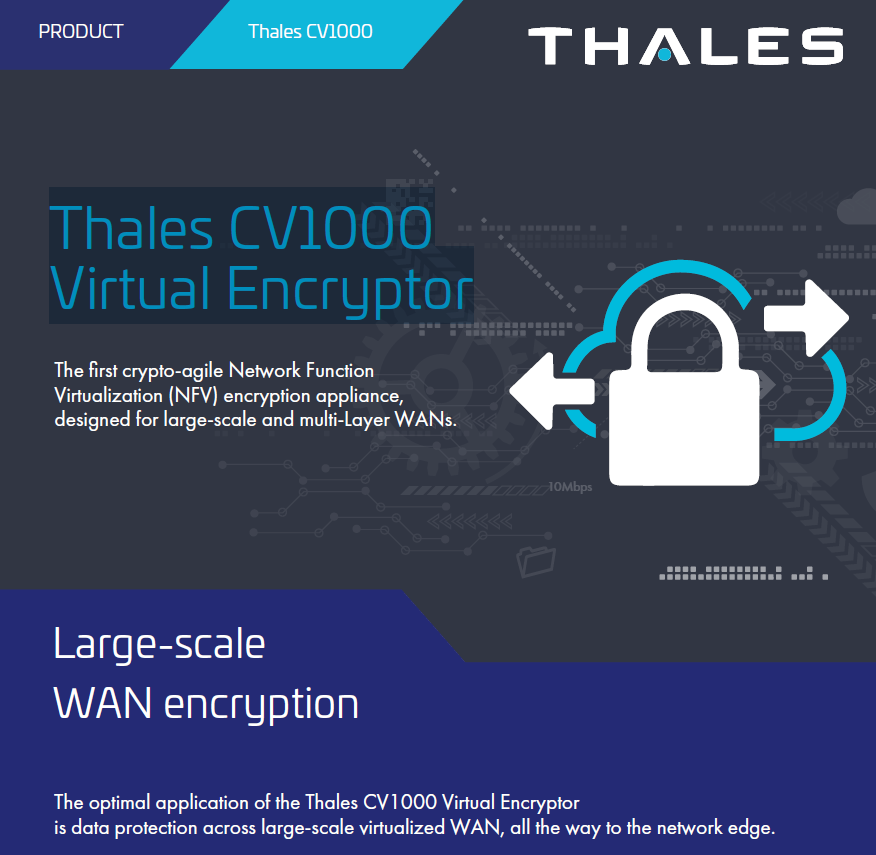
| Infographic: Thales CV1000 Virtual Encryptor | Network Encryption | network-encryption | ||
| Integrated Data Discovery and Classification with Enhanced Protection Product Brief | CipherTrust | ciphertrust | ||
| Introduction to Thales’ CipherTrust Enterprise Key Management Solutions | CipherTrust | ciphertrust | ||
| ISC and Thales TCT HSM Solution Brief | HSM Integrations, Integrations | hsm-integrations integrations | ||
| KeySecure G160 Product Brief | KeySecure | keysecure | ||
| Luna as a Service Solution Brief | Cloud Security, HSM, Luna as a Service, Luna Credential System | cloud-security hsm luna-as-a-service luna-credential-system | ||
| Luna Credential System & UiPath RPA: Addressing Federal CAC/PIV Requirements with PKI Authentication | Luna Credential System, Video | luna-credential-system video | ||
| Luna Credential System Product Brief | Luna Credential System | luna-credential-system | ||
| Luna Credential System Video | Luna Credential System, Video | luna-credential-system video | ||
| Luna G5 for Government HSM Product Brief | HSM | hsm | ||
| Luna Network HSM Product Brief | HSM | hsm | ||
| Luna PCIe HSM Product Brief | HSM | hsm | ||
| Luna Tablet HSM Product Brief | HSM | hsm | ||
| Microsoft Azure Advanced Data Protection Solution Brief | CipherTrust Integrations, Cloud Security, Integrations | ciphertrust-integrations cloud-security integrations | ||
| Multi-Factor Authentication for CipherTrust Transparent Encryption | CipherTrust | ciphertrust | ||
| NetApp and Thales TCT Solution Brief | CipherTrust, CipherTrust Integrations, Integrations | ciphertrust ciphertrust-integrations integrations | ||
| Network Encryption Family Overview Brief | Network Encryption | network-encryption | ||
| Nutanix and Thales TCT Solution Brief | CipherTrust, CipherTrust Integrations, Integrations | ciphertrust ciphertrust-integrations integrations | ||
| On Demand Master Class: Zero Trust Beyond the Buzzword | Webcast, Zero Trust | webcast zero-trust | ||
| On Demand Webinar – Intelligence Community: Cyber Security is National Security | Cloud Security, Webcast, Zero Trust | cloud-security webcast zero-trust | ||
| On Demand Webinar: Best Practices for Cloud Data Protection | Cloud Security, Webcast | cloud-security webcast | ||
| On Demand Webinar: Best Practices for Data Visibility | CipherTrust, Webcast | ciphertrust webcast | ||
| On Demand Webinar: Building a Root of Trust to Secure the Most Sensitive Data | HSM, Webcast | hsm webcast | ||
| On Demand Webinar: Complementing Splunk: Balancing Big Data Benefits & Big Risks | CipherTrust, CipherTrust Integrations, Webcast | ciphertrust ciphertrust-integrations webcast integrations | ||
| On Demand Webinar: Fireside Chat: Data Protection for Multi-Domain Operations | CipherTrust, Webcast | ciphertrust webcast | ||
| On Demand Webinar: Getting to Compliance with the National Security Memo on Cybersecurity | Compliance, Webcast | compliance webcast | ||
| On Demand Webinar: How To Issue Hardware-Based Identity Credentials To Software Robots | Luna Credential System, RPA, Webcast | luna-credential-system rpa webcast | ||
| On Demand Webinar: No-Excuse Defenses Against Supply Chain Attacks | Votiro, Webcast | votiro webcast | ||
| On Demand Webinar: Rapid Protection for Teradata Database and Big Data Environments | CipherTrust, Webcast | ciphertrust webcast | ||
| On Demand Webinar: Shifting the Mindset from “Breach Prevention” to “Acceptance” | Webcast, Zero Trust | webcast zero-trust | ||
| On Demand Webinar: The Key Pillars for Protecting Sensitive Data | CipherTrust, Webcast | ciphertrust webcast | ||
| Panasas PanFS and Thales TCT CipherTrust Manager Solution Brief | CipherTrust Integrations, Integrations | ciphertrust-integrations integrations | ||
| Product Brief: SafeNet OTP Display Card | Identity & Access Management | identity-access-management | ||
| Product Brief: eToken PASS OTP Authenticator | Identity & Access Management | identity-access-management | ||
| Product Brief: IDCore 230/3230 | Identity & Access Management | identity-access-management | ||
| Product Brief: Imperva Application Security | Imperva | imperva | ||
| Product Brief: Imperva Data Risk Analytics | Imperva | imperva | ||
| Product Brief: Imperva Data Security Fabric | Imperva | imperva | ||
| Product Brief: Imperva Data Security Fabric – Unstructured Data Discovery and Classification | Imperva | imperva | ||
| Product Brief: Imperva WAF Hardware Appliances | Imperva | imperva | ||
| Product Brief: Imperva Web Application Firewall Gateway | Imperva | imperva | ||
| Product Brief: SafeNet Authentication Service Private Cloud Edition | Identity & Access Management | identity-access-management | ||
| Product Brief: SafeNet eToken 5110 series | Identity & Access Management | identity-access-management | ||
| Product Brief: SafeNet eToken 5300 Series | Identity & Access Management | identity-access-management | ||
| Product Brief: SafeNet IDPrime 930/931 Series | Identity & Access Management | identity-access-management | ||
| Product Brief: SafeNet IDPrime PIV | Identity & Access Management | identity-access-management | ||
| Product Brief: SafeNet OTP 110 Token | Identity & Access Management | identity-access-management | ||
| Product Brief: SafeNet Trusted Access | Identity & Access Management | identity-access-management | ||
| Product Brief: Thales FIDO2 Devices | Identity & Access Management | identity-access-management | ||
| Product Demo: Protecting AWS S3 Buckets: AWS KMS vs Transparent Encryption COS S3 from Thales | Cloud Security, Video | cloud-security video | ||
| Protecting Data with Thales CipherTrust Manager and Dell PowerEdge Server | CipherTrust, CipherTrust Integrations, Integrations | ciphertrust ciphertrust-integrations integrations | ||
| Protecting Data with Thales Key Management and Dell VxRail HCI System | CipherTrust Integrations, Integrations | ciphertrust-integrations integrations | ||
| Quantum Enhanced Keys Solution Brief | HSM, Quantum | hsm quantum | ||
| Quantum Resistant High Speed Network Encryption | CSfC, Network Encryption | csfc network-encryption | ||
| Redhat and Thales TCT Solution Brief | HSM Integrations, Integrations | hsm-integrations integrations | ||
| Research Study: Security Weaknesses in Data in Motion Identified in Cybersecurity Survey | Network Encryption, White Paper | network-encryption white-paper | ||
| Robotic Process Automation Industry Insight | Luna Credential System, RPA | luna-credential-system rpa | ||
| RPA Cryptographic Authentication — Thales TCT and Blue Prism | LCS Integrations, Luna Credential System, RPA | lcs-integrations luna-credential-system rpa integrations | ||
| SafeNet IDPrime PIV | Identity & Access Management | identity-access-management | ||
| Secure Edge Data with Multi-Layer Encryption through HPE Edgeline and Thales TCT CipherTrust k160 | CipherTrust, CipherTrust Integrations, Integrations | ciphertrust ciphertrust-integrations integrations | ||
| Securing Infoblox DNSSEC Implementations with Thales TCT’s Luna Network HSM Solution Brief | HSM Integrations, Integrations | hsm-integrations integrations | ||
| Securing UiPath Credential Stores with Luna Vault Solution Brief | LCS Integrations, Luna Credential System | lcs-integrations luna-credential-system integrations | ||
| Security Management Center Product Brief | Network Encryption | network-encryption | ||
| sKey3250 Product Brief | Identity & Access Management | identity-access-management | ||
| Smart Card 650 Product Brief | Identity & Access Management | identity-access-management | ||
| Solution Brief: Best Security Practices for milCloud Data Migration | Cloud Security | cloud-security | ||
| Solution Brief: CipherTrust Cloud Key Management for Oracle Cloud Infrastructure | CipherTrust | ciphertrust | ||
| Solution Brief: Data Protection Solutions for the Edge | ||||
| Solution Brief: Data Risk Analytics Overview | Imperva | imperva | ||
| Solution Brief: Imperva Data Security Fabric Overview | Imperva | imperva | ||
| Solution Brief: Imperva for Splunk Optimizations | Imperva | imperva | ||
| Solution Brief: Top 10 Reasons to Migrate to the CipherTrust Data Security Platform For KeySecure Customers | CipherTrust, KeySecure | ciphertrust keysecure | ||
| Solution Brief: Top 10 Reasons to Migrate to the CipherTrust Data Security Platform For Vormetric Customers | CipherTrust, Vormetric | ciphertrust vormetric | ||
| Solution Brief: Votiro + Office 365 | ||||
| Solution Brief: WAAP Checklist | Imperva | imperva | ||
| SureDrop Product Brief | SureDrop | suredrop | ||
| Thales Authentication Family Brief | Identity & Access Management | identity-access-management | ||
| Thales High Speed Encryption Solutions Family Overview | Network Encryption | network-encryption | ||
| Thales IDPrime FIDO 2.0 Smartcard Demo | Identity & Access Management, Video | identity-access-management video | ||
| Thales Secures SAP Data with Dell in Any-premises | CipherTrust, CipherTrust Integrations | ciphertrust ciphertrust-integrations integrations | ||
| Thales Security Solutions for Google Workspace | CipherTrust Integrations | ciphertrust-integrations integrations | ||
| Thales TCT and Splunk Solution Brief | CipherTrust, CipherTrust Integrations, Integrations | ciphertrust ciphertrust-integrations integrations | ||
| Thales TCT CipherTrust Enterprise Key Management and Dell Technologies | CipherTrust, CipherTrust Integrations | ciphertrust ciphertrust-integrations integrations | ||
| Thales TCT CSfC Capabilities Solution Brief | CSfC | csfc | ||
| Thales TCT HSM Product Family Overview Brief | HSM | hsm | ||
| Thales TCT Luna Hardware Security Solutions for Microsoft Certificate Services | HSM Integrations, Integrations | hsm-integrations integrations | ||
| Thales TCT Luna HSMs for Commercial Solutions for Classified (CSfC) Solution Brief | Compliance, CSfC, HSM | compliance csfc hsm | ||
| Thales TCT Solutions for the NSM on Improving Cybersecurity of NSS Solution Brief | Compliance | compliance | ||
| Thales TCT Solutions for White House Executive Order on Cybersecurity | Compliance | compliance | ||
| Thales TCT: Protecting the Most Vital Data from the Core to the Cloud to the Field | Video | video | ||
| Thales Trusted Cyber Technologies Product Overview | ||||
| Thales Trusted Cyber Technologies Solutions for Continuous Diagnostics and Mitigation DEFEND | Compliance | compliance | ||
| The Dual Faces of Quantum Computing: Opportunities and Threats in National Security | Quantum, Video | quantum video | ||
| Top 10 Reasons CipherTrust Intelligent Protection will Protect Your Data & Reduce Your Risk | CipherTrust | ciphertrust | ||
| Top 10 Reasons for Protecting Your Organization with CipherTrust Data Security Platform | CipherTrust | ciphertrust | ||
| Top 5 Reasons for Choosing SafeNet eToken Fusion Series | Identity & Access Management | identity-access-management | ||
| Top 5 Ways to Comply with the White House EO on Cybersecurity – Part 1 – Setting the Stage | Compliance, Video | compliance video | ||
| UiPath RPA Cryptographic Authentication with Luna Credential System | LCS Integrations, Luna Credential System | lcs-integrations luna-credential-system integrations | ||
| Video: CipherTrust Data Discovery & Classification | Video | video | ||
| Video: Securing 5G Private Networks with Thales High Speed Encryptors | Network Encryption, Video | network-encryption video | ||
| Video: Thales High Speed Encryptors Demo | Network Encryption, Video | network-encryption video | ||
| Virtual CipherTrust Manager Product Brief | CipherTrust | ciphertrust | ||
| VMware and Thales Deliver Secure Hyper-Converged Infrastructure Solution Brief | CipherTrust, CipherTrust Integrations, Integrations | ciphertrust ciphertrust-integrations integrations | ||
| VMware and Thales Deliver Secure Virtual Machine Encryption Solution Brief | CipherTrust, CipherTrust Integrations, Integrations | ciphertrust ciphertrust-integrations integrations | ||
| VMware and Thales TCT Integration Brief | CipherTrust | ciphertrust | ||
| Vormetric Data Security Platform Product Brief | Vormetric | vormetric | ||
| Votiro | Secure File Gateway Partners | secure-file-gateway-partners | ||
| Votiro + Office 365 Solution Brief | Votiro | votiro | ||
| Votiro Secure File Gateway for Email | Votiro | votiro | ||
| Votiro Secure File Gateway for Web Applications | Votiro | votiro | ||
| Votiro Secure File Gateway vs Secure Email Gateway Solution Brief | Votiro | votiro | ||
| White Paper: 10 Things Every Web Application Firewall Should Provide | Imperva | imperva | ||
| White Paper: Best Practices for Cloud Data Protection and Key Management | Cloud Security | cloud-security | ||
| White Paper: Best Practices for Cryptographic Key Management | HSM, White Paper | hsm white-paper | ||
| White Paper: Best Practices for Implementing the White House Executive Order on Improving the Nation’s Cybersecurity Infrastructure | Compliance, Identity & Access Management | compliance identity-access-management | ||
| White Paper: Best Practices for Secure Cloud Migration | Cloud Security | cloud-security | ||
| White Paper: Best Practices for Securing Network Function Virtualization Environment | Network Encryption | network-encryption | ||
| White Paper: CipherTrust Data Security Platform Architecture | CipherTrust | ciphertrust | ||
| White Paper: CipherTrust Transparent Encryption | CipherTrust | ciphertrust | ||
| White Paper: CJIS Data-in-Transit Encryption Standards | Compliance, Network Encryption | compliance network-encryption | ||
| White Paper: Continuous Diagnostics and Mitigation: Data Protection & Assurance | Compliance | compliance | ||
| White Paper: Data Protection at the Edge | Edge Solutions, White Paper | edge-solutions white-paper | ||
| White Paper: Ethernet WAN Solutions Compared | Network Encryption, White Paper | network-encryption white-paper | ||
| White Paper: High Assurance Encryption for Healthcare Network Data | Compliance, White Paper | compliance white-paper | ||
| White Paper: High Speed Encryption Solutions Across MPLS Networks | Network Encryption, White Paper | network-encryption white-paper | ||
| White Paper: HIPAA Compliance Checklist | Compliance | compliance | ||
| White Paper: How to Choose a Secrets Management Solution | CipherTrust, White Paper | ciphertrust white-paper | ||
| White Paper: Key Management | CipherTrust, White Paper | ciphertrust white-paper | ||
| White Paper: MACsec for WAN and High Assurance Encryptors | Network Encryption, White Paper | network-encryption white-paper | ||
| White Paper: Malicious Macros | Votiro, White Paper | votiro white-paper | ||
| White Paper: Meeting U.S. Government requirements for phishing-resistant MFA | Identity & Access Management | identity-access-management | ||
| White Paper: Network Independent Encryption | Network Encryption, White Paper | network-encryption white-paper | ||
| White Paper: NIST 800-53 Mapping to CipherTrust Data Security Platform | CipherTrust, White Paper | ciphertrust white-paper | ||
| White Paper: NIST 800-57 Recommendations for Key Management Requirements Analysis | Compliance, White Paper | compliance white-paper | ||
| White Paper: NIST Cybersecurity Framework and Ransomware Prevention Guidance Mapping | Compliance | compliance | ||
| White Paper: Own and Manage Your Encryption Keys | CipherTrust, White Paper | ciphertrust white-paper | ||
| White Paper: Prevent Ransomware Attacks from Disrupting Your Agency with the CipherTrust Platform | White Paper | white-paper | ||
| White Paper: Protecting sensitive data in and around SAP HANA | CipherTrust, CipherTrust Integrations, White Paper | ciphertrust ciphertrust-integrations white-paper integrations | ||
| White Paper: Quantum Resistant Code Signing Secured by Hardware Security Modules | HSM, Quantum, White Paper | hsm quantum white-paper | ||
| White Paper: Roots of Trust | HSM, White Paper | hsm white-paper | ||
| White Paper: Secure Multicast Transmission | Network Encryption, White Paper | network-encryption white-paper | ||
| White Paper: Securing Network-Attached HSMs | HSM, White Paper | hsm white-paper | ||
| White Paper: Securing SD-WAN | Network Encryption, White Paper | network-encryption white-paper | ||
| White Paper: Securing the Keys to the Kingdom with Splunk and Thales | CipherTrust, CipherTrust Integrations, Integrations, White Paper | ciphertrust ciphertrust-integrations integrations white-paper | ||
| White Paper: Splunk and Thales Industry Standard Protection for Your Log Data | CipherTrust, CipherTrust Integrations, Integrations, White Paper | ciphertrust ciphertrust-integrations integrations white-paper | ||
| White Paper: Splunk Optimization by Imperva | Imperva | imperva | ||
| White Paper: Thales TCT Solutions for CMMC | Compliance | compliance | ||
| White Paper: The Case for Centralized Multicloud Encryption Key Management | CipherTrust, Cloud Security, White Paper | ciphertrust cloud-security white-paper | ||
| White Paper: The Importance of KMIP Standard for Centralized Key Management | CipherTrust, White Paper | ciphertrust white-paper | ||
| White Paper: The Key Pillars for Protecting Sensitive Data in Any Organization | CipherTrust, White Paper | ciphertrust white-paper | ||
| White Paper: Top Five Ways to Address Requirements in National Security Memo on Improving Cybersecurity of National Security Systems | Compliance, White Paper | compliance white-paper | ||
| White Paper: Understanding Data Security for SAP | CipherTrust, CipherTrust Integrations, White Paper | ciphertrust ciphertrust-integrations white-paper integrations | ||
| White Paper: WAAP Buyers Guide | Imperva, White Paper | imperva white-paper | ||
| Zero Trust Solutions from Thales TCT Solution Brief | Zero Trust | zero-trust | ||
| Zero Trust: Top 5 Tips | Video, Zero Trust | video zero-trust |