Thales Trusted Cyber Technologies (TCT), a business area of Thales Defense & Security, Inc., is a trusted, U.S. provider of cybersecurity solutions dedicated to U.S. Government. We protect the government’s most vital data from the core to the cloud to the edge with a unified approach to data protection. Our solutions reduce the risks associated with the most critical attack vectors and address the most stringent encryption, key management, and access control requirements.
We help federal agencies protect and manage sensitive data and identities through our encryption, key management, authentication and access management solutions. Our unified data protection solutions address the government’s most pressing cybersecurity challenges.
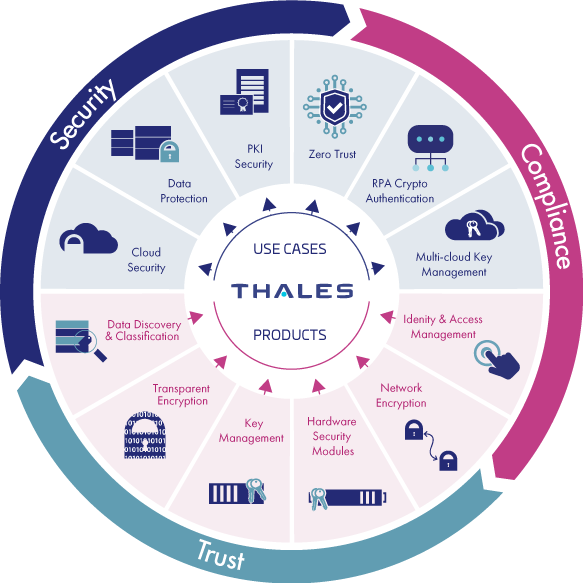
Our solutions deliver the same level of security whether deployed in enterprise, cloud, or edge environments. We enable agencies to meet their immediate cybersecurity needs while investing in a solution that provides robust security, a growing ecosystem, and the scalability needed to build a trusted framework for the future.

ZERO TRUST
Address foundational pillars of Zero Trust with our authentication, encryption, and key management solutions.

CLOUD SECURITY
Safely store sensitive data in the cloud with our cloud-independent encryption, key management, and authentication solutions.
DATA PROTECTION
Protect data residing in databases, applications, files, and storage containers with our solutions that provide granular encryption, role-based access control, and key lifecycle management.

PKI SECURITY
Store, protect and manage crypto keys used to secure sensitive data and critical applications with FIPS 140-2 Level 3 hardware security modules that meets government U.S. supply chain requirements.
IDENTITY & ACCESS MANAGEMENT
Control access to sensitive data and protect user identities with our multi-factor authentication solutions.

NETWORK ENCRYPTION
Encrypt data in transit everywhere through our comprehensive solutions that protect data, video, and voice without compromising security or performance.

ROBOTIC PROCESS AUTOMATION
Maintain robot credentials in a centralized hardware device that is securely accessible by endpoints in a distributed network.

QUANTUM
Deploy crypto-agile products to combat emerging technical threats as the age of the quantum computer looms.

Edge Security
Apply the same level of security deployed in the core and the cloud to edge environments.
