Turning on the equivalent of full-disk encryption for a public cloud provider is simple. However, managing data security in a multi-cloud environment with different cloud storage options quickly gets complex. Thales TCT offers advanced multi-cloud Bring Your Own Encryption (BYOE) tools to secure your data and reach compliance rapidly and effectively.
Most cloud service and leading encryption providers use the same encryption technique: Advanced Encryption Standard, or AES. However, encrypting data is only a starting point. To truly protect your data, you need to consider the threats you’re protecting against, managing encryption keys and access controls across multiple cloud providers.
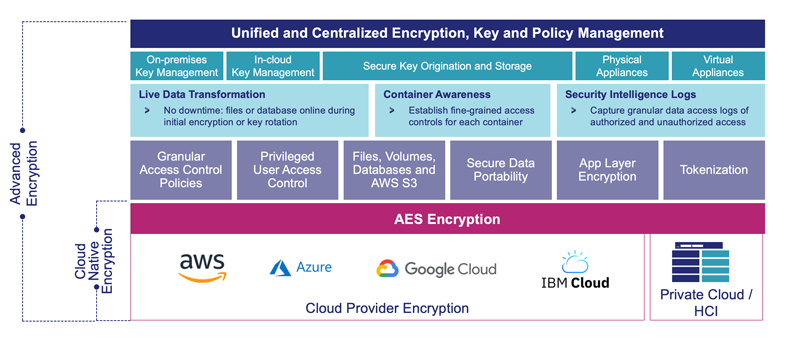
Compared to the native encryption solutions available from cloud providers, Thales TCT BYOE through CipherTrust Data Security Platform delivers:
- High-performance AES encryption enhanced by hardware acceleration and granular access control policies, including privilege user access control. BYOE controls who, through what process and at specified times, can see specific data.
- An architecture that secures unstructured files, structured databases, and big data environments and also enables users to migrate data between cloud environments and on-premises servers without the time and cost of decryption. For additional granular controls and meeting a larger breadth of regulations, easily add format preserving or traditional encryption or tokenization to applications using RESTful APIs or the industry’s most powerful and secure encryption libraries.
- BYOE extensions enable use of data during encryption and rekeying operations with patented Live Data Transformation or, to isolate and secure container environments by creating policy-based encryption zones. BYOE monitors and logs file access to accelerate threat detection with Security Intelligence Log integration with popular SIEM tools.
- Simplified key management across on-premises and multi-cloud deployments by centralizing control on CipherTrust Manager.
