SAP provides the operational lifeblood of many enterprises with SAP modules providing essential functions that run the gamut from enterprise resource ...
Read MoreOn the surface, encrypting the database instance using SAP native encryption would appear to be sufficient to protect data at rest within the SAP HANA...
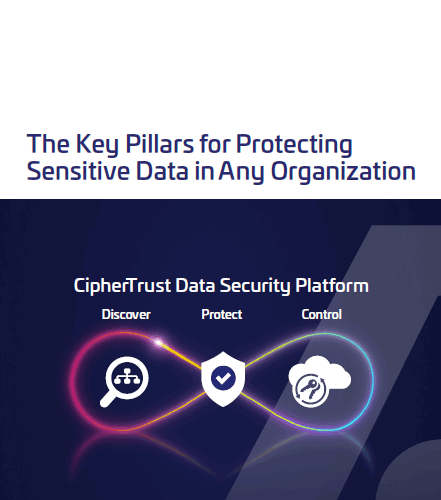
Read MoreToday, protecting sensitive data is a fundamental requirement in virtually every business. What’s also nearly universal is this: operations and securi...
Read MoreCloud consumers face a choice: using the cloud service provider’s (CSP) encryption or bringing their own encryption. Cloud providers make their native...
Read MoreThis white paper outlines the challenges of data security in this age of data proliferation. It also provides strategies to discover and classify your...
Read MoreThis paper examines the use of Splunk as the platform to collect and index machine data from virtually any source, regardless of its location. Then, w...
Read MoreLearn About Thales Trusted Cyber Technologies Solutions for Continuous Diagnostics and Mitigation DEFEND
Read MoreThis white paper looks back at the evolution of encryption and key management systems, and examines the key challenges faced by IT teams around encryp...
Read MoreThales Trusted Cyber Technologies (TCT) data security and access management solutions provide some of the most essential components of the cybersecuri...
Read MoreThe Cybersecurity Maturity Model Certification (CMMC) is the Department of Defense’s (DoD) newest verification mechanism designed to ensure that cyber...
Read More