The exponential growth of big data, cloud services, and use of remote data centers has resulted in an unprecedented movement of data throughout networks. Transmitted data is increasingly valuable and bandwidth demands are constantly increasing.
Agencies need effective, affordable network encryption solutions that can mitigate the risks without slowing down the network.
Level up network security
Agencies don’t have to choose between security and speed. Thales’ comprehensive network encryption solutions use encryption at Layers 2, 3, and/or 4 to secure data in transit without slowing down the network.
Ensuring maximum throughput with minimal latency, the Thales High Speed Encryptors allow you to protect data, video, voice, and metadata from eavesdropping, surveillance, and overt and covert interception.
Source: Thales CSP
What high speed encryptors can do for your agency
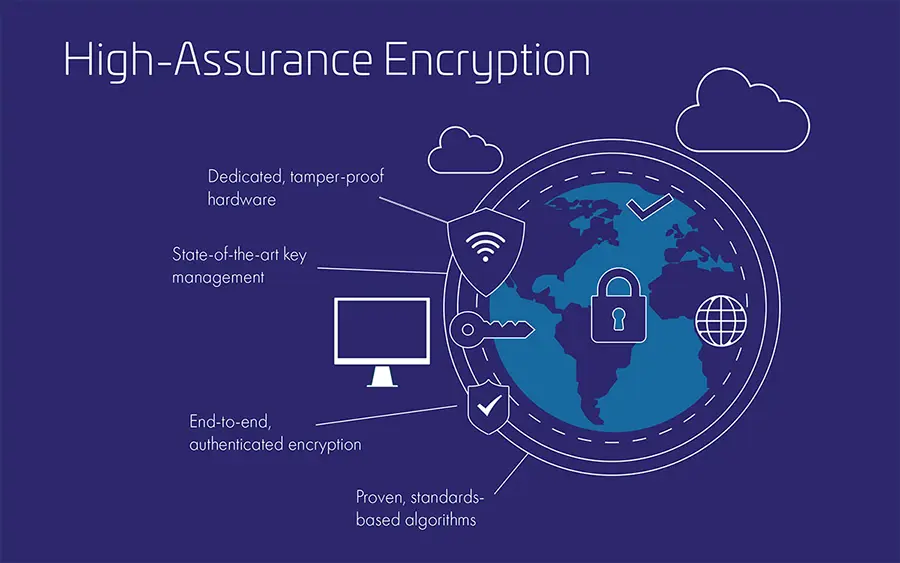
Strongest Key Management
HSEs have an integrated CA, protected in a tamper responsive hardware boundary. All keys are generated and protected in FIPS 140-3 Level 3 chassis.
Access Controls
Apply granular, least-privileged user access policies that protect data from external attacks and misuse by privileged users.
Automated Updates
All HSE traffic keys are updated every hour (default) and are zeroized if under security critical alarm.
Bandwidth Efficiency
HSEs use a certified security protocol to provide 2x bandwidth optimization over legacy security protocols such as IPsec or MACsec.
Minimize Latency
HSEs utilize a cut-through architecture that minimizes latency and jitter and provides consistency among all data frame sizes.
Reduce Complexity
Complex environments increase surface attack areas. HSEs are set and forget—NO active management or regular patching/updates required.
Strongest Solution
HSEs provide fully authenticated end-to-end encryption and are 3rd-party certified to the highest commercial standards.
(AES-GCM 256, EDSA/ECDH, SHA)
Crypto Agile
As standards and threats evolved a crypto agile platform is required. HSEs use FPGA technology to update security without performance compromise.
Meet Compliance Mandates
Because HSEs are crypto agile, you’ll always be compliant with current standards and regulations.
(e.g. GDPR, HIPAA, NIST, CJIS)
42.2% savings per protected Gb
Miercom Independent Laboratory reports Thales High Speed Encryptors demonstrate superior performance and cost-efficiency compared to traditional IPsec encryption.
High Speed Encryption Benefits
Data in motion security at speeds up to 100 Gbps
Prepare for Quantum and other threats
Say goodbye to legacy encryption solutions that are:
- Outdated like IPSec and MACsec (15-25 years old)
- Not designed for modern networks such as SDN, 5G and cloud
- Fail to provide end-to-end security or compliance
- Cause network limitations
Agencies using Thales High Speed Encryption solutions get out-of-the-box Post-Quantum Cryptography (PQC) and support for customization and advanced security features.
Source: Thales CSP
Achieve compliance
Organizations must remain in compliance with applicable data protection regulations or face security risks and fines for non-compliance.
Thales High Speed Encryption solutions provide advanced audit reporting and support for a broad range of compliance needs – FIPS, DoDIN APL, NATO, CJIS, HIPAA, NERC, and many more.
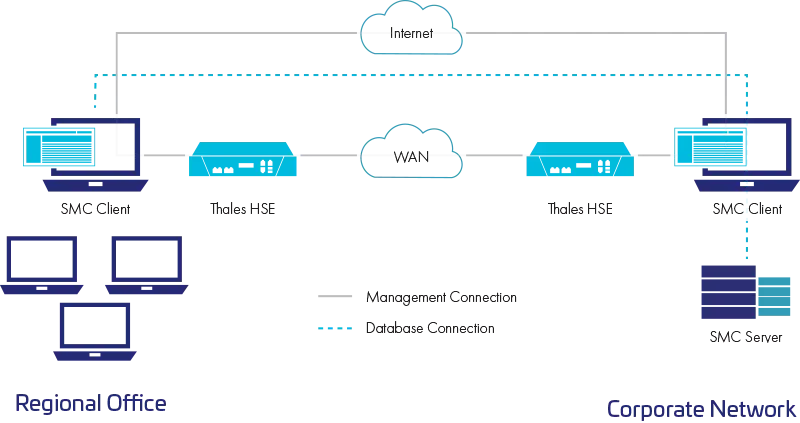
Plan for business continuity and disaster recovery
Sensitive and regulated data is constantly traversing the network from headquarters to branch offices. Organizations need real-time transmissions of sensitive data to disaster recovery sites, on premises and in the cloud.
Thales High Speed Encryption solutions ensure the information remains totally secure without slowing down the network and interfering with other business functions.
CN SERIES NETWORK ENCRYPTORS AND MANAGEMENT PLATFORMS

CN4000 Series
Small form factor for remote locations.
- 100 Mbps – 1 Gbps Ethernet Encryptor
- Certified, high-performance

CN6000 Series
Optimizes private networks and DC interconnects.
- 1 Gbps to 4×10 Gbps Ethernet Encryptor
- Rack-mountable, fully redundant robust design

CN7000 Series
Platform agnostic network encryption.
- Platforms: in-vehicle encyptor (-40C to 70C Fanless), rack mount enterprise hub, industrial control edge encryption, milspec (extremely rugged, IP67 waterproof and dustproof

CN9000 Series
Designed for next gen datacenters and core networks.
- Multipoint 100 Gbps Encryption
- Fully interoperable with CN product range

Network Encryptor Management Platform
Management solutions to administer security across heterogeneous network.
- Management solutions to administer security across heterogeneous networks
Recommended Resources
Frequently asked questions
What is the performance impact of Thales HSEs on the network?
Thales High Speed Encryption (HSE) solutions are designed to minimize performance impact on the network. They operate at the physical limit of the network, reaching up to 100 Gbps without any noticeable bandwidth reduction. Unlike traditional solutions like IPsec, which rely on tunneling and add bulk to data packets, HSE employs a thin layer of encryption that minimizes drag. Independent tests have proven HSE’s superior performance and low latency compared to legacy solutions like IPsec.
How does Thales HSE compare to other network encryption solutions?
What are the advantages of Thales HSE verses other network encryption solutions?
Thales HSE offers several advantages over other network encryption solutions:
- Higher Speed: Thales HSE can encrypt data at speeds of up to 100 Gbps, with superior efficiency and bandwidth utilization, as compared to legacy solutions like IPsec and MACsec.
- Greater Flexibility: Thales HSE is more flexible and can be used to encrypt a wider range of traffic types (Layers 2, 3, and 4).
- Stronger Security: Thales HSE provides stronger security by using certified, standards-based encryption, aligned with security best practices, and also supports quantum-resistant algorithms.
- Lower Latency: Thales HSE has a lower latency than IPsec and MACsec.
How does Thales HSE compare to legacy encryption solutions like IPsec?
Legacy solutions like IPsec were built for specific tasks and often rely on tunneling, which adds extra layers of encapsulation and slows down data transfer. Thales HSE, with its lean architecture and certified standards-based encryption, minimizes overhead and ensures data travels at maximum speed, even while encrypted. IPsec only operates at Layer 3, whereas Thales HSE offers Transport Independent Mode (TIM) network layer independent (Layer 2, Layer 3, and Layer 4) and protocol agnostic data in motion encryption. TIM being a tunnel-free solution is able to traverse network layers 2,3, and 4.
How does Thales HSE differ from MACsec?
MACsec is suitable for point-to-point connections and simpler network setups but lacks the flexibility and scalability of Thales HSE. Managing complex networks with MACsec can be cumbersome and potentially lead to security gaps. MACsec only operates at Layer 2, whereas Thales HSE offers Transport Independent Mode (TIM) network layer independent (Layer 2, Layer 3, and Layer 4) and protocol agnostic data in motion encryption. TIM being a tunnel-free solution is able to traverse network layers 2,3, and 4. Also, while MACsec can offer high speeds, it may not be as efficient in terms of overhead, especially for smaller data packets.
How does Thales HSE work with TLS?
Thales HSE and TLS serve different purposes and can complement each other, working together to provide comprehensive data protection. TLS operates at the application layer, securing specific tasks like web browsing or email. Thales HSE, on the other hand, secures the entire network infrastructure, regardless of the applications running on top.
How do I manage the device?
Thales offers centralized management for the entire suite of Thales network encryptors. The management platforms for its network encryptor can be configured as a Certificate Authority for encryptors running on the network, simplifying key management, and ensuring secure communication.
How reliable are Thales HSEs?
Thales HSEs are engineered for high reliability. The systems are built with no single point of failure, meaning that if one component malfunctions, others seamlessly take over. This ensures continuous operation and uninterrupted security, even in case of hardware issues. The devices are proven to have a high MBTF (mean time between failures), and with fewer or even no problems over your equipment’s extensive lifetime, you benefit from lower costs related to repairs or downtime. In fact, our devices are considered “set and forget” by our customers.
How secure is data-in-motion encryption?
Data-in-motion encryption is a highly secure method of protecting data as it travels across a network. It uses strong encryption algorithms to transform data into an unreadable format, making it impossible for unauthorized parties to access the information.
What algorithms are supported?
Thales HSE solutions are crypto-agile, supporting a wide range of encryption algorithms, including customizable encryption for various elliptic and custom curves, and post-quantum cryptography to enable Quantum-safe solutions today, and into the future. For specific algorithm support, please refer to the latest product briefs on our website.
What type of attacks can be prevented?
Data-in-motion encryption with Thales HSE solutions can effectively prevent various types of attacks, including:
- Man-in-the-middle attacks: Where attackers intercept and potentially alter communications between two parties.
- Eavesdropping: Unauthorized listening to or interception of network traffic.
- Data breaches: Attempts to steal sensitive information transmitted over the network, including Harvest Now, Decrypt Later (HNDL) attacks. By encrypting the data, these attacks are rendered ineffective, as the attacker cannot access or understand the information without the proper decryption keys