Protect Root Encryption Keys used by Applications and Transactions from the Core to the Cloud to the Edge.
Hardware Security Modules (HSMs) are dedicated crypto processors designed to protect the cryptographic key lifecycle. HSMs serve as trust anchors that protect an organization’s cryptographic infrastructure by securely managing, processing, and storing cryptographic keys inside a hardened, tamper resistant device.
Luna T-Series HSMs are the choice for government agencies when storing, protecting and managing cryptographic keys used to secure sensitive data and critical applications. Meeting government mandates for U.S. Supply Chain, the high-assurance, tamper-resistant Luna T-Series HSMs are designed, developed, manufactured, sold, and supported in the United States.

Security First Company
- U.S. Foundation (development, manufacturing, personnel, facilities)
- Strong security practices
Security and Compliance
- Address compliance requirements with FIPS 140-2 L3 and CNSS Approval
- Keys and certificates automatically generated and stored in hardware
Scalability and High Availability
- Ability to have multiple applications share the same hardware
- Easy to add new applications – no new HSM required
- Ability to cluster HSMs to avoid single point of failure
Government Approval & Reference
- CNSS approval for TCT HSMs on National Security Systems
- NCCoE reference architecture for TLS Server Certificate Management
- Trusted supplier to U.S. Govt.
Partner Ecosystem
- Out-of-the-box integrations with their applications
- Existing integrations that align with partner’s future plans
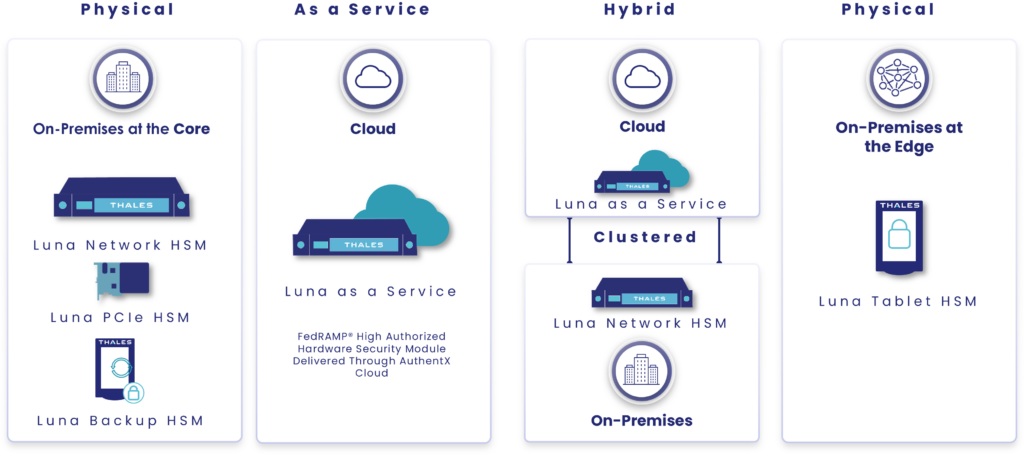
Root of Trust Where You Need It
Available Models
 |
 |
 |
 |
|
|---|---|---|---|---|
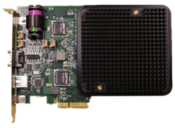
LUNA PCIE
|
LUNA NETWORK HSM
|
LUNA TABLET HSM T-300 |
LUNA as a SERVICE |
LUNA BACKUP HSM |
| Embedded HSM that protects cryptographic keys and accelerates sensitive cryptographic operations | Network-attached HSM that protects encryption keys used by applications in on-premise, virtual, and cloud environments | USB-attached HSM that is ideal for storing root cryptographic keys in an offline key storage device | Cloud-based HSM delivered through XTec’s FedRAMP High authorized AuthentX Cloud | Offline backup HSM |
| Use Case: Securing Custom Applications | Use Cases: PKI, SSL/TLS, Code Signing, Certificate Signing and Validation, Document Signing Transaction Processing, DB Encryption, Smart Card Issuance | Use Case: Offline Root CAs | Use Case: Cloud Smart Root-of-Trust, Anchoring Applications Across Multiple Cloud Providers | Use Case: Securely backup high value cryptographic key material |
| Learn More | Learn More | Learn More | Learn More | Learn More |
Resources
| Image | Title | Link |
|---|---|---|
| CTO Sessions On Demand: Best Practices for Implementing Quantum-Resistant Security | ||
| CTO Sessions Webcast On Demand: Building a Root of Trust in How to Secure the Most Sensitive Data | ||
| CTO Sessions Webcast On Demand: HSM Boot Camp – A Guide to HSM Deployments from the Core to the Cloud to the Edge | ||
| CTO Sessions: Cloud HSM Best Practices | ||
| CTO Sessions: Quantum-Resistant Code Signing | ||
| Luna as a Service Solution Brief | ||
| Luna G5 for Government HSM Product Brief | ||
| Luna Network HSM Product Brief | ||
| Luna PCIe HSM Product Brief | ||
| Luna Tablet HSM Product Brief | ||
| On Demand Webinar: Building a Root of Trust to Secure the Most Sensitive Data | ||
| Product Brief: Luna T-Series Backup HSM | ||
| Quantum Enhanced Keys Solution Brief | ||
| Solution Brief: Thales TCT Luna HSMs for Commercial Solutions for Classified (CSfC) | ||
| Solution Brief: Thales TCT Post-Quantum Cryptography Implementation | ||
| Thales TCT HSM Product Family Overview Brief | ||
| Washington Technology Commentary: Why federal agencies must act now on post-quantum cryptography | ||
| White Paper: Best Practices for Cryptographic Key Management | ||
| White Paper: Quantum Resistant Code Signing Secured by Hardware Security Modules | ||
| White Paper: Roots of Trust | ||
| White Paper: Securing Network-Attached HSMs |