Securely leverage your enterprise data
AI apps and agents are being deployed across the organization and with access to sensitive data, often without adequate security – introducing new risks. Thales AI Security Fabric runtime security solutions enables organizations to adopt AI confidently while protecting sensitive data, maintaining compliance, and preserving brand trust.
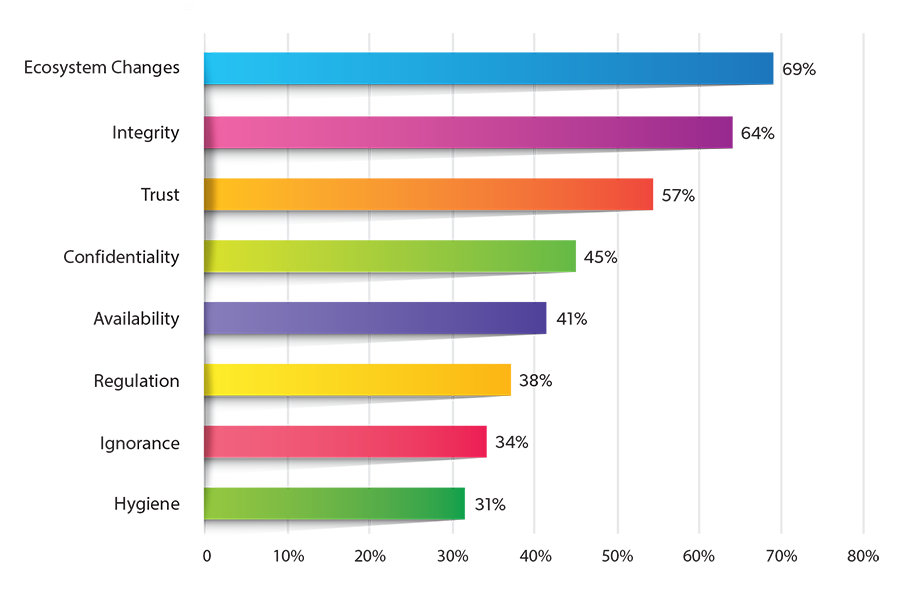
What is blocking rapid and safe AI GenAI adoption?
The most concerning risks of GenAI security include integration of new systems into an already complex Hybrid IT and the integrity, trust and confidentiality powering AI.
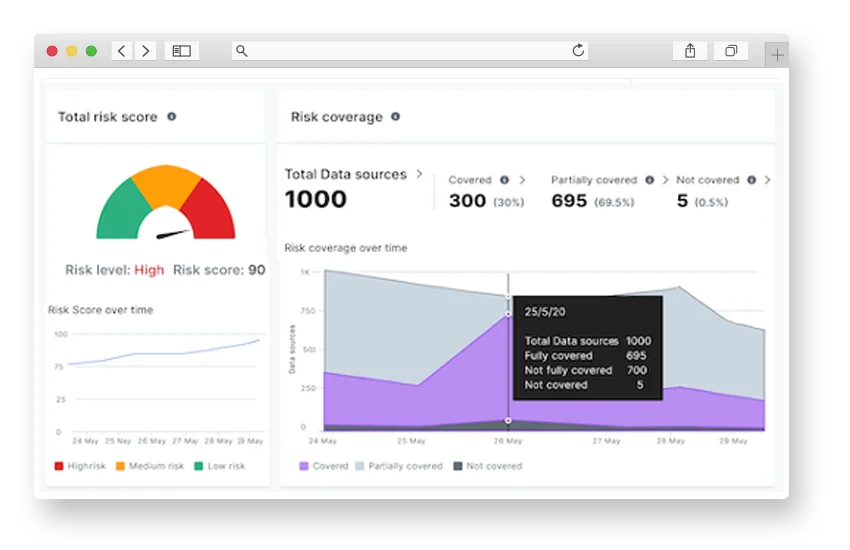
Unlock business value with AI data security posture management
AI thrives on large datasets. But for AI to be effective for business, it must incorporate enterprise data that may include sensitive or proprietary data.
Thales AI runtime security solutions allow organizations to improve their AI data security posture management, allowing Agentic AI and Gen AI access to datasets while protecting sensitive data based on policy.
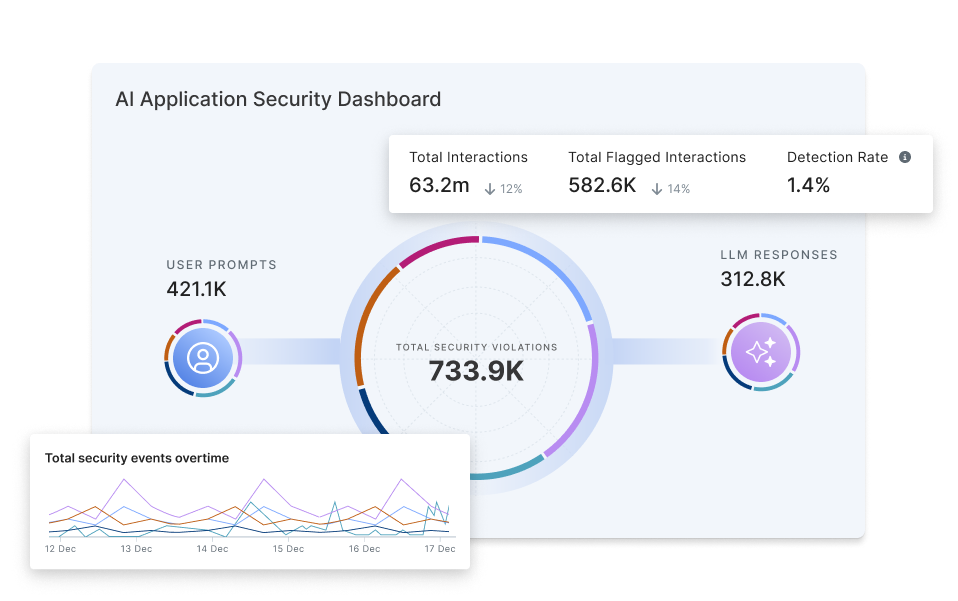
Address the top LLM vulnerabilities
Attacks on AI applications and models is on the rise.
From reducing the risk of data poisoning and model manipulation to identifying and blocking common prompt injection techniques, Thales AI runtime security solutions address a majority of the OWASP GenAI Security Project’s Top 10 threats to LLMs by uncovering vulnerabilities, protecting data and applications, and detecting and stopping malicious activity in real time.

Logo and materials © OWASP GenAI Security Project, used under the project’s branding and license guidelines.
Accelerate AI adoption while maintaining compliance
AI adoption is a priority for a majority of organizations, but the pressure to integrate AI fast is overwhelming already overextended security and compliance teams.
Thales AI runtime security solutions automate key security functions by enforcing custom policies aligned with desired security requirements and security or privacy regulations.
Thales AI Security Fabric Runtime Security Solutions

Featured Resources
Resources
| Image | Title | Link |
|---|---|---|
| CTO Sessions: Word on the Street – 2026’s Top Tech Trends | ||
| Video: A Roadmap for Securing AI Systems and Data | ||
| Solution Brief: Thales Retrieval Augmented Generative (RAG) AI Data Protection Solutions | ||
| On Demand ATARC Webinar: Intersection of Quantum, AI, and Security | ||
| CTO Sessions On Demand: When AI Learns to Breach and Quantum Learns to Decrypt – The Endgame | ||
| CTO Sessions Webcast On Demand: Intersection of Quantum, AI and Security | ||
| CTO Session Webcast On Demand: Intersection of AI and Security | ||
| White Paper: Protect LLMs with CipherTrust Transparent Encryption | ||
| FedNewsNetwork Video Interview: Preparing for the intersection of AI, quantum computing | ||
| FedNewsNetwork Commentary: Preparing for the intersection of AI, quantum computing |